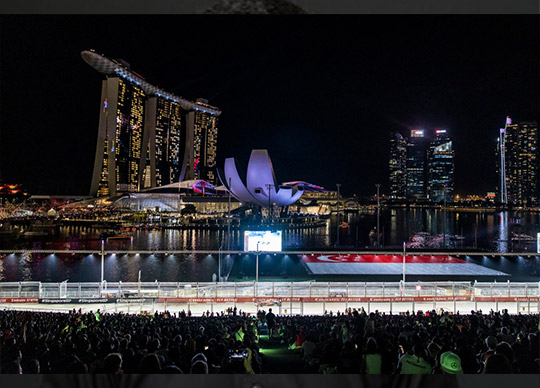

Image 1 F1 main: Photo Credit: Formula 1 Singapore Airlines Singapore Grand Prix 2022.
Written By Jane Lo, Singapore Correspondent.
“400 gigabytes of data is generated per event, quite sizable when it all adds up, “said Douglas Goodridge (Chief Information Officer, Williams Racing), at Acronis #CyberFit Day Singapore 2022 (29th September 2022) as the city geared up for the return of world’s original night race after a 2-year hiatus.
Winding around historic and architectural landmarks by the Marina Bay and the downtown core, the 5.063 kilometers of track, illuminated with almost 1,600 floodlights, was once again transformed into a spectacular sight for the Formula 1 Singapore Airlines Singapore Grand Prix 2022.
Data is King
Tracking the performance of their teams over the race weekend, the fans may appreciate that today’s F1 car is highly instrumented, networked and connected, with hundreds of sensors in each car that generate millions of data points over a race weekend.
But casual observers may not realise that it is a data driven sport where the technological ability to measure, analyse and react on data is crucial to the team’s winning strategy.
There is the “data within the car”, there is the “telemetry information that needs driver inputs”, data about “how the systems in the car are running, such as temperatures, pressures”, Goodridge said.
These data are captured and analysed real-time in a continuous feedback loop to deliver that fraction of a second advantage in performance over competitors.
Indeed, on race day, while the fans’ attention is riveted on the racetrack action, another battle is playing out behind the scenes.
Here is where engineers and technicians, working with innovative technologies and the team’s race director and headquarters (the “HQ”, for Williams Racing this is Grove, Oxfordshire), race to extract insights from the millions of data points and adjust the race strategy in real-time.
“Data itself is not a new thing, has been going on in F1, and evolving over a period of time. However, we now have huge amounts of data, generated by trackside and back over at HQ”, Goodridge noted.
The quest for perfection continues post-race and during practice runs, up till the race day.
Metrics culled from the chassis, tires and throughout the engines are fed into models and simulations – often said to be as advanced as those used in the Aerospace industry technology.
Combined with historical information, these data are harnessed in predictive models to make design changes to the car before the next race.
Goodridge, pointing out how data is exploited to inform decision making, said: “the important thing is to treat data in a holistic manner.”
“Instead of having an isolated view of say, the car, or the trackside operations, and everything that goes on in the factory, we look at everything as one,” he said.
This is to help understand “how we can leverage the data” and “correlate the data” to “ensure that we have the correct outcome,” he explained.
In this relentless drive to maximise performance, the gigantic amount of data tracked, transmitted, stored and analysed is clearly an important intellectual property.
Securing such a significantly valuable asset is therefore of paramount importance.
Williams Racing CIO (Douglas Goodridge), Acronis CEO (Patrick Pulvermueller), Acronis CISO (Kevin Reed) recently offered their insights into data protection in F1 at Acronis #CyberFit Day Singapore 2022.
While principles to protect the asset (private circuits, encryption, segregation policies, lengthy gardening leave for senior team members to minimise leaks) are standard industry best-practices, the discussions offered insights into practices unique to F1.

Image 2 panel edit: From Left: Acronis CEO (Patrick Pulvermueller); Acronis CISO (Kevin Reed); Williams Racing CIO (Douglas Goodridge).
Here are some highlights.
Cyber threat landscape
Data being such a “crown jewel” for a F1 team is highly attractive to threat actors seeking to exploit any weaknesses in the team’s protection strategy for monetary gains or otherwise.
Indeed, F1 like any other industry, is not immune to say, insider threats. There was the 2007 spygate where a rival team reportedly sought access to a competitor’s data via an insider, or the 2014 Marussia incident where an employee inadvertently visited a malicious website which introduced a trojan into the team’s computer network.
It is also vulnerable to the waves of ransomware attacks that targeted organisations ranging from global multinationals to small medium size enterprises.
When asked about the current cyber threat landscape, Reed said “it is the same, but getting worst.”
Goodridge added, “as you use technology to enable department and sections of the businesses that traditionally were not technologically focused – marketing is one example, social media is another – you are broadening the threat landscape.”
In defending against the increasing threats, Goodridge highlighted the “responsibilities of understanding where your boundaries are.”
Traditional perimeter security and the Zero Trust model
Digitalisation, along with the expanding threat landscape also prompt a “think about perimeter security and the Zero Trust model,” he said.
Today’s explosion of “IoT” devices means that data is increasingly stored, accessed, retrieved, and transmitted remotely – a situation further complicated by the Covid-19 pandemic.
Cyber protection relying on the traditional perimeter security, distinguishing between the “trusted” (inside the perimeter) devices and the “untrusted” (outside), struggles to respond to these challenges.
The Zero Trust model, on the other hand, applies the blanket rule of verifying all devices, including those considered to be inside the trusted perimeter.
Nevertheless, regardless of protection measures, Goodridge stressed the need for “understanding where that data sits, how valuable it is and understanding overall, the threat at risk level.”
Physical security and protection
However, protection is also about physical security, as much as the cyber one.
Typically, a F1 team transports 50 tonnes of equipment – ranging from furniture, panelling to IT and garage equipment, and up to 100 personnel per race, as the team globetrotters to the 22 race locations.
The complex logistics of packing, transporting, and unpacking to set up the team’s home base and garage is a highly tuned plan where each equipment is essential to chasing that incremental boost in speed.
With the latest technological innovations on car design kept under wraps until as late as the flag-off, it is no surprise that physical security is of high priority – as evident from the presence of hundreds of guards – perhaps more so than a typical large entertainment event.
More interestingly, there is the additional consideration of physical protection integral to the overall security.
Goodridge shared that the IT equipment are exposed to variations in temperature and the elements (such as build-up of sand and dust in locations where there are no air-conditioned facilities) as they traverse the world.
Protection of these mobile IT infrastructure against damage, executed in compliance with FIA (Fédération Internationale de l’Automobile) requirements, is another challenge not to be underestimated.
Data recovery and back-ups
With the rising sophistication of threats and the old adage of “no 100% security”, data protection naturally extends to more than proactive defensive measures.
Building in “redundancy” and “resiliency”, according to Pulvermueller, are necessary, and “mean-time-to-restore” is key where back-ups are deployed.
Although these are arguably industry best practices and data restoration under most circumstances is highly stressful, the time factor in a sport synonymous with speed vastly raises the stakes.
Moreover, while ransomware remains an ever-present threat that can strike on race day, downtime during design and development could also cost the team the vaunted podium finish.
Furthermore, as with all sports, F1 teams have historically used biometric data to monitor athletes’ fitness and performance – the collection and processing of which are set out in the FIA “guidelines for the collection and usage of biometric data in motor sport.”
So, “data retention” and “de-duplication” in back-ups will also need to adhere to FIA’s guidelines (as well as EU’s GDPR), according to Pulvermueller and Reed.
Last words
“Data is the forefront of everything we do, F1 is a data driven sport,” Goodridge said.
“We are learning and evolving forward – that is the key for us to how we need to use data more efficiently in the future,” he added.
But malicious actors are undoubtedly evolving as well. In protecting against the rising sophistication of the adversaries seeking to steal, impair and destroy the crown jewel, “learn from the mistakes of others,” Reed advised.

Image 3 Group: The Singapore Formula 1 2022 Williams Racing garage tour, guided by the Williams racing team.





