

“Mr Teo Chee Hean (Senior Minister and Coordinating Minister for National Security) speaking at the SICW2019 Opening Ceremony. Photo Credit: SICW 2019”
2019 commemorates 200 years since Sir Stamford Raffles’s landing on Singapore, the historic event many Singaporeans fondly associate with his sighting of a lion and the naming of the island as “The Lion City” or Singapura.
Travel accounts and early maps also mentioned “Barxingapara” (1502), “Sinca Pora” (1607), Sincapura” (1690), reflecting the shifting references – from a gateway, a strait, to a settlement.
The varying etymology stemmed from the significance of Singapore’s waterways as a maritime artery in the region, very much vulnerable to pirate attacks, political and military incursions.
The Anglo-Dutch Treaty in 1824 settled the long-running territorial and trade disputes in South East Asia between then maritime superpowers Great Britain and the Netherlands.
Tackling the threats of pirates, who were “absolutely swarming” (according to historic records) and highly organized, to kidnap, raid, and plunder, incurred considerably more time and efforts.
Choosing a route was a security decision.
Today, this strategic location that connects the Indian Ocean to the South China Sea is now an international financial, shipping and aviation hub, housing critical systems that transcend national borders, such as global payment systems, port operations systems and air-traffic control systems.**
**Singapore’s Cyber Security Strategy
“Just as the pioneers faced danger and adversity on the seas to bring wealth and prosperity to this corner of the world, so shall we continue that journey in cyberspace,” said David Koh (Commissioner of Cybersecurity and Chief Executive Cyber Security Agency of Singapore) in his Welcome message to the 5th edition of the Singapore International Cyber week.
“Authored by Dr Mark van Staalduinen and Yash Joshi of TNO (the Netherlands Organisation for applied scientific research) with TNO and CSA (Cyber Security Agency of Singapore) experts, the study was developed by as an outcome of the bilateral IoT Security Workshop between Singapore and the Netherlands in The Hague on 18 May 2017 and the Global Forum on Cyber Expertise (GFCE) meeting in Brussels on 30 May 2017.
It was executed under the MoU between CSA and the National Cyber Security Centre (NCSC) of the Netherlands signed 14 July 2016 in Singapore.”
Today, Cyber is the new frontier and “like the pirates of old, there are those who would exploit cyberspace for malicious purposes,” he said.
“Cities around the world have ushered in the era of digital transformation. Singapore is no different, as we work towards our vision of a Smart Nation,” he added.
“This brings about the phenomenon of manufacturing every type of device to be “smart”. From traffic cameras to lamp posts and even the most mundane of devices like rice cookers and baby monitors are now part of the “Internet of Things” or IoT.” he explained.
The threats of this rapid proliferation are multi-fold:
The connected devices, as origins of compromise, expand the surface vulnerable to attacks; acting as carriers, they enable the propagation of viruses; and as connectors, their integration with the physical world raise the potential to cause direct physical harm.
We hear more at Singapore International Cyber Week (SICW 1st Oct – 3rd Oct 2019, Suntec Convention and Exhibition Centre) and Singapore International Energy Week (SIEW 29th Oct –1st Nov, Marina Bay Sands Convention Centre).
Cyber Security of Devices in Smart Nation
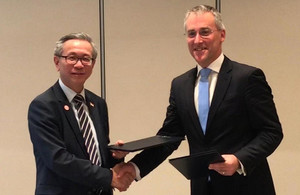
“David Koh, CEO of Singapore’s Cyber Security Agency, and Ciaran Martin, Head of the UK’s National Cyber Security Centre. Photo Credit: British High Commission Singapore.”
An example of an IoT threat was the Mira malware that launched the DDoS (distributed denial-of-service) disrupting the internet for 8 hours in 2016.
This incident was cited in a “IoT Security Landscape” study report (IoT or the Internet-of-Things), commissioned jointly by Singapore and the Netherlands, launched at the SICW 2019.
Mirai compromised hundreds of thousands of devices to jam the servers at Dyn’s data centres. Unable to respond to legitimate requests, the servers forced the shut-down of 80 websites, including Amazon and Google.
Some may argue that Mirai or the SingHealth incidents caused no real damage – only, for example, mere inconveniences from completing an Amazon transaction, or breach of personal sensitive information.
Or even in the case of fingerprint spoofing for illegitimate authentication of biometrics, a mere case of identity theft.
But there are genuine safety threats:
- FDA’s (U.S. Food and Drug Administration) recall of a pacemaker manufacturer in 2017, for potential cybersecurity issues which would allow an unauthorized user to “modify programming commands to the implanted pacemaker, which could result in patient harm from rapid battery depletion or administration of inappropriate pacing” (that is, abnormal regulation rate of the device);
- Smart Cars with “vehicle-to-anything” connectivity (vehicle-to-vehicle/ consumer/ infrastructure/ pedestrian) where safety necessitates robust cybersecurity measures to mitigate dangerous navigation caused by unintended bugs or hacking attempts;
- The “Triton” malware which infiltrated a Middle Eastern oil and gas petrochemical facility in December 2017 and triggered a safety system shutdown.
Healthcare, transport, energy sectors are part of the 11 Critical Information Infrastructure (CII) that are responsible for the continuous delivery of essential services in Singapore – the others include government, infocomm, aviation, maritime, banking and finance, water, security and emergency, and media.
As these sectors are digitally transformed to build a Smart Nation, devices are being networked for planning and tracking, remote operation, surveillance, predictive maintenance.
This digital fabric increasingly powering our daily interaction can be easily disrupted by a communication breach or a malfunctioned program.

“Dr Janil Puthucheary (Senior Minister of State (SMS), Ministry of Communications and Information, and SMS in-charge of Cybersecurity) added at the International Common Criteria Conference (ICCC) during the SICW 2019. For the first time, SICW 2019 host the flagship international forum for the Common Criteria industry, an annual event for the international IT security product evaluation and certification industry. Global thought leaders, certification bodies, evaluation labs, product developers and policy makers focus on the specification, development, evaluation, certification and approval of Common Criteria in IT security products. Photo Credit: SICW 2019”
Security-by-design
Security-by-design, in which device manufacturers and developers embed security measures during the design phase, aims to mitigate threats that cause such disruption.
This principle was highlighted in the Operational Technology (OT) Cybersecurity Masterplan, announced by Mr Teo Chee Hean (Senior Minister and Coordinating Minister for National Security) at the SICW 2019 Keynote.
Besides boosting training and establishing an OT Cybersecurity Information Sharing and Analysis Centre, the plan also encourages OT equipment manufacturers and service providers to adopt cybersecurity-by-design in the developmental phase.
The principle was also referenced in the Joint Statement on bilateral cooperation between Singapore and the UK on the IoT during the SICW 2019:
“… we want to ensure that internet-connected devices have security built in by design and the public and industry are protected against related security threats, such as cyberattacks, theft of personal data and risks to physical safety… ”

“Mr Boris Balacheff (HP Fellow & VP, Chief Technologist for Security Research and Innovation, HP Labs Security Lab) at ICCC 2019.”
Implementing this principle requires harmonized standards for the plethora of devices independently developed by different manufacturers. For example, Miria’s exploitation of devices’ simple default passwords could have, to some degree, be mitigated with pre-agreed a “no default password” standard.
ISO/IEC 15408, or the Common Criteria (“CC”), a gold standard for IT security evaluation for over 20 years, remains today “the de facto standard for IT security product certification around the world”, said Dr Janil Puthucheary (Senior Minister of State (SMS), Ministry of Communications and Information, and SMS in-charge of Cybersecurity) at the International Common Criteria Conference (ICCC) during SICW 2019.
“It advocates for devices to be secure-by-design, taking cyber security considerations into the product design and its subsequent life cycle, allowing customers and companies to identify products that have been rigorously tested, verified and certified”, he said.
A labelling scheme deriving from a scheme such as CC (or other international standards) would promote users’ awareness of vulnerabilities of their devices. This could influence better buying decisions, and in turn could reduce the surface vulnerable to attacks such as Mirai.
Recognised as a Common Criteria Certificate Authorising Nation in January 2019, Singapore joins the other 30 nations in the Common Criteria Recognition Arrangement whereby CC certificates issued by an authorised nation are mutually recognized across all member nations.
Dr Puthucheary also stressed that “better product assurance, especially for network-connected devices, is going to be important. If we can adopt these product evaluation and certification regimes, such as CC, it will give the kind of assurance benchmarked at internationally-recognised standards, to strengthen IT security for our government, Smart Nation as well as the digital economy.”

“From Left:
Moderator: Chintan Ganatra, Energy, Utilities and Resources Industry Leader, PwC South East Asia Consulting, Singapore
Shanul Rashid, Custodian Engineer – Instrument & Control, PETRONAS, Malaysia
Fuad Al-Ansari, Vice President, Information Technology Division, ADNOC, UAE
Christophe Romatier, Product Line Director, Connected Performance Services, Honeywell UOP, USA
Bradley G. Houk, Senior Engineering Advisor & Open Process Automation Project Manager, ExxonMobil, USD
N. Pasupathy Prasad, Director Strategic Accounts, Astoria Solutions, Singapore”
“Choosing a device has become a security decision”
For sure, we rely more and more on personal devices such as medical implants and mobile phones, or business printers and computers for collection, analysis, transmission and storage of information.
Moreover, the traditionally isolated Operational Technology systems are increasingly linked to internet with industrial sensors, routers, and more. At the Singapore International Energy week, Faud Al-Ansar (VP IT Division Abu-Dubai National Oil Company) noted, for the energy sector, that Operational Technology (OT) and Information Technology (IT) are converging so rapidly that mitigating security flaws could become main concerns in this race to integrate systems.
Indeed, as pointed out by Mr Boris Balacheff (HP Fellow & VP, Chief Technologist for Security Research and Innovation, HP Labs Security Lab) at the SICW 2019, ““organizations have not traditionally included cyber-security requirements in IT equipment procurement, but this is to change, because we clearly see a rise in attackers focusing on exploit lower layers of device hardware and firmware. Indeed, we can say that in the 21st century, choosing a device has become a security decision.”
As we journey towards Smart Nation, security is paramount to protect the confidentiality, integrity and authenticity of the devices underpinning our critical infrastructures.





