
Just a week after Bitdefender Antispam Labs reported on a phishing campaign targeting financial and personal details of Bank of America customers, cybercriminals brought out their big guns in a new, more dangerous attack on Standard Chartered Bank users.
The ongoing malicious campaign seeks to infect recipients’ devices with FormBook malware under the guise of an attached ZIP archive file that allegedly contains payment advice from the bank.
The campaign was deployed on July 13 and is still active. According to our researchers, the campaign has been primarily using IP addresses from Vietnam for malware distribution, targeting users in the UK (24%), US (22%), South Korea and South Africa (8%). A few emails also reached recipients in Germany, Czech Republic, Russia, Romania and Australia.
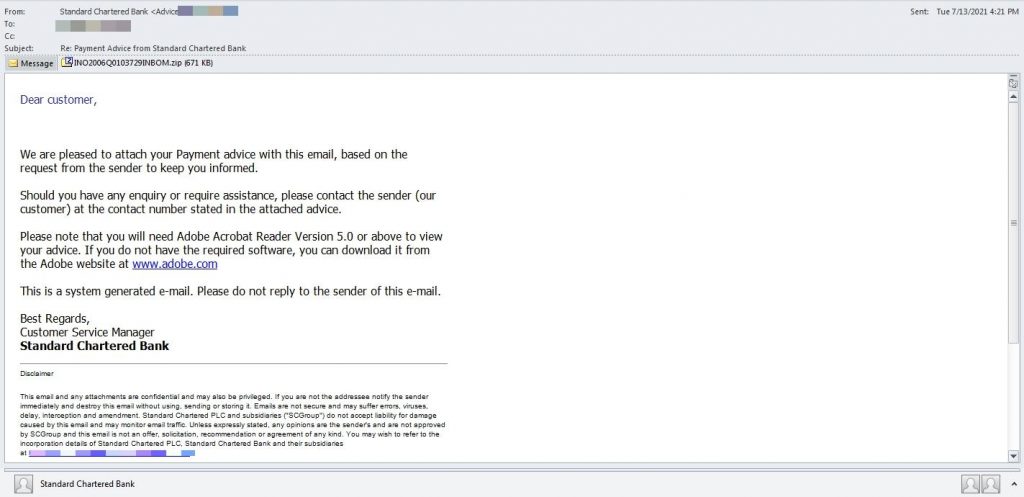
“We are pleased to attach your Payment advice with this email, based on the request from the sender to keep you informed,” the fake email reads. “Should you have any enquiry or require assistance, please contact the sender (our customer) at the contact number stated in the attached advice.Please note that you will need Adobe Acrobat Reader Version 5.0 or above to view your advice. If you do not have the required software, you can download it from the Adobe website.”
This malicious software is an info stealer that harvests user credentials from browsers, messengers and emails. It also hosts clipboard monitoring and network traffic-sniffing capabilities, making it a dangerous spy tool for threat actors.
However, FormBook can execute commands on the infected device, including rebooting or shutting down systems, downloading and running files, and unpacking archive files.
This monitoring and spyware tool has been heavily marketed on underground forums since 2016, growing in popularity with the help of malware-as-a-service providers who rent it to cybercriminals on a subscription basis. Its easy-to-use interface, password-stealing capabilities and regular updates make this Trojan a suitable cyber weapon to defraud victims.
The FormBook Trojan designed to steal personal data from victims’ computers is predominantly distributed via phishing emails with malicious payloads hiding in DOC and XLS files, PDFs, and archive files such as ZIP, RAR and RAR ISOs.
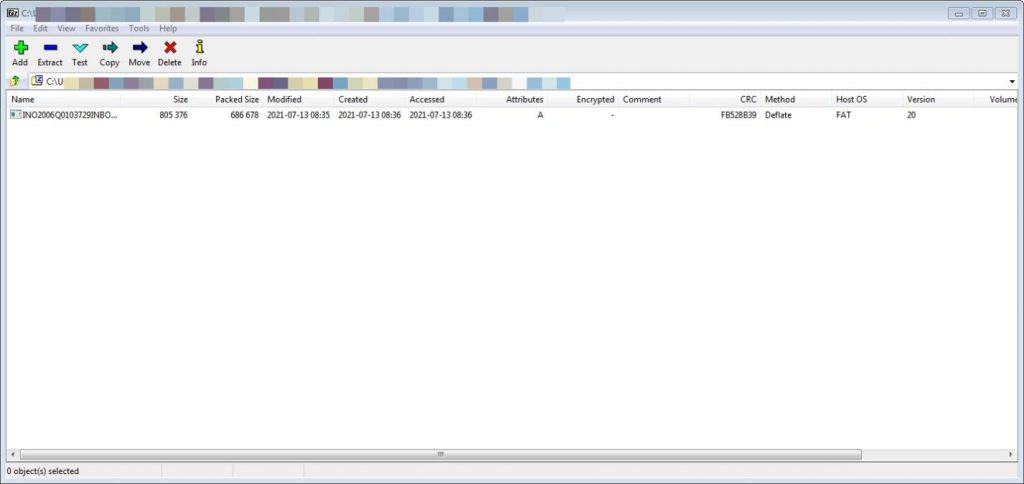
Bitdefender detects the INO2006Q0103729INBOM.zip as Trojan.GenericKD.37229317.
To prevent device compromise, you should verify the validity of messages before accessing attachments and install a security solution on your device. The notion that a financial provider is sending you an archive attachment should immediately raise suspicion.
Note: This article is based on technical information provided courtesy of Bitdefender Labs






