
Group-IB has detected a dump containing details for nearly 400,000 payment card records uploaded to a popular darknet cardshop on April 9. The database was comprised almost entirely of the payment records related to banks and financial organizations in South Korea and the US. It should be noted that it is the biggest sale of South Korean records on the dark web in 2020, which contributes to the growing popularity of APAC-issued card dumps in the underground. The provenance of this data remains unknown. Group-IB has informed proper authorities in South Korea and the US so they could take necessary steps, and continues to work closely with its partners in these countries to mitigate the impact of an incident.
During cardshop monitoring Group-IB Threat Intelligence system has detected a database under the name “SCARFACE-DISCOUNT-SALE-5USD (fresh skimmeD): USA (STATES MIX + few EU) TR1 + TR2/TR2, VALID 30-40%, uploaded 2020-04-09 (NON-REFUNDABLE BASE)” released and put up for sale on April 9. Joker’s Stash – the infamous underground marketplace – put a USD 1,985,835 price tag on the set, at USD 5 apiece, and announced that dump had 30-40% valid rate.
“Fig. 1 – Advertisement for the new base on Joker’s Stash”
The total number of records exposed is 397,365. Even though the database name didn’t include a single mention of South Korea, South-Korean card details made up the majority in the newly released batch – roughly 49.9% (198,233 items valued at USD 991,165.) were from South Korea’s banks and financial organizations. 49,3% were related to US banks and financial organizations. While American card dumps have traditionally been most commonly traded in the dark web, the South Korean payment card details are a very rare commodity in the underground. The newly released database marks the biggest sale for South Korean card dumps in 2020, the latest massive upload of credit and debit card details from this country occurred more than 8 months ago.

“Fig. 2 – Sale of South Korean-issued card dumps in the underground in 2019”
Group-IB found out that over the past few years APAC-issued card dumps have been offered for sale increasingly often and starting from 2019 became the second most popular target in the underground by the number of massive abnormal spikes in their sales, surpassed only by US-issued dumps – all-time “champion” on this market. The growing supply of APAC-issued cards dumps pressures the prices down making them more available. In recent years, Group-IB reported on a number of instances originating from APAC, such as the sale of the record-breaking database holding more than 1.3 million credit and debit card dumps of mainly Indian banks’ customers in October 2019. Pakistan-issued dumps have been also traded in large volumes in February 2019 and November 2018. Remarkably, card dumps do not necessarily get compromised in a card-issuing country, the data can be snatched when a card owner travels overseas to a country where advanced payment security measures, such as EMV, are not widely implemented, and uses an infected Point-of-Sale (POS) terminal.
The database of the credit and debit card details mainly contains Track 2 information – the data stored on the magnetic stripe of a card, which includes the bank identification number (BIN), the account number, expiration date and may also include the card verification value (CVV). The Track 2 data (also referred to as card dumps) is used for card-present transactions and usually comes from infected POS terminal, from ATM skimmers or breached merchant’s payment system. However, in this case, the source of the stolen data remains unknown.
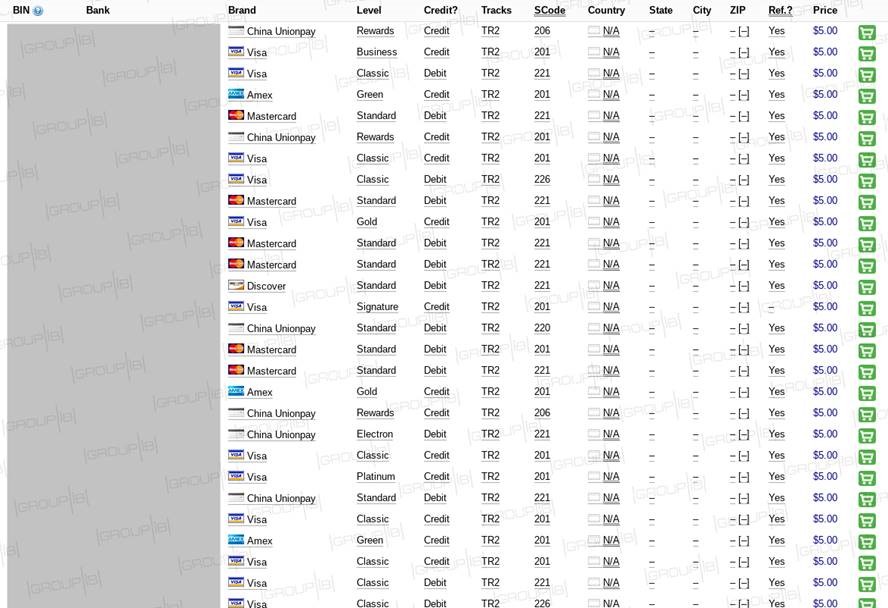
“Fig. 3 – Payment card details released on April 9”
Group-IB has already provided the information about the incident to national CERTs and financial sharing organizations in the US and South Korea so they could take all necessary steps to mitigate the risks, and continues outreach to the affected parties through its partners in South Korea and the US.
“Even though there is not enough information in this dump to make online purchases, fraudsters who buy this data can still cash out stolen records,” says Shawn Tay, senior threat intelligence analyst at Group-IB. “If a breach is not detected promptly by the card-issuing authority, crooks usually produce cloned cards (“white plastic”) and swiftly withdraw money via ATMs or use cloned cards for illicit in-person purchases. Constant underground monitoring for compromised personal and payment records of their customers gives banks and financial organizations the ability to mitigate risks and further damage by quickly blocking stolen cards and track down the source of the breach.”





